Focused on Solutions
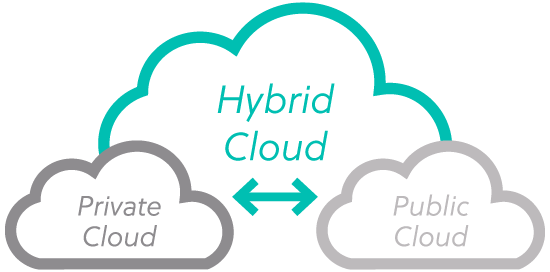
We don’t do Cloud just one way. We’ll help you choose the right Cloud option for the right applications based on such factors as compliance requirements, your business strategy and the capabilities of your mission-critical applications.
.png)